Source: Electronic Frontier Foundation
Automated license plate readers (ALPRs) are high-speed, computer-controlled camera systems that are typically mounted on street poles, streetlights, highway overpasses, mobile trailers, or attached to police squad cars. ALPRs automatically capture all license plate numbers that come into view, along with the location, date, and time. The data, which includes photographs of the vehicle and sometimes its driver and passengers, is then uploaded to a central server.
Vendors say that the information collected can be used by police to find out where a plate has been in the past, to determine whether a vehicle was at the scene of a crime, to identify travel patterns, and even to discover vehicles that may be associated with each other. Law enforcement agencies can choose to share their information with thousands of other agencies.
Taken in the aggregate, ALPR data can paint an intimate portrait of a driver’s life and even chill First Amendment protected activity. ALPR technology can be used to target drivers who visit sensitive places such as health centers, immigration clinics, gun shops, union halls, protests, or centers of religious worship.
Drivers have no control over whether their vehicle displays a license plate because the government requires all car, truck, and motorcycle drivers to display license plates in public view. So it’s particularly disturbing that automatic license plate readers are used to track and record the movements of millions of ordinary people, even though the overwhelming majority are not connected to a crime.
How ALPRs Work
Automated license plate readers can be broadly divided into two categories.
Stationary ALPR cameras

Photo by Mike Katz-Lacabe (CC BY)
These are installed in a fixed location, such as a traffic light, a telephone pole, the entrance of a facility, or a freeway exit ramp. These cameras generally capture only vehicles in motion that pass within view.
If multiple stationary ALPR cameras are installed along a single thoroughfare, the data can reveal what direction and what speed a car is traveling. If the data are stored over time, they can reveal every time a particular plate has passed a given location, allowing the government to infer that the driver likely lives or works close by.
Stationary cameras can sometimes be moved. For example, surveillance vans or truck trailers can be outfitted with ALPR systems and then parked at strategic locations, such as gun shows or political rallies.
ALPR cameras are often used in conjunction with automated red-light and speed enforcement systems, and also as a means of assessing tolls on roads and bridges.
Mobile ALPR cameras

Photo by Mike Katz-Lacabe (CC BY)
These are often attached to police patrol cars, allowing law enforcement officers to capture data from license plates as they drive around the city throughout their shifts. In most cases, these cameras are turned on at the beginning of a shift and not turned off again until the end of the shift. Also, private vendors like Vigilant Solutions capture plate data with mobile ALPRs and then sell that data to police agencies and others.
In addition to capturing images of passing vehicles, mobile ALPR cameras are effective at capturing license plates of parked cars. For example, a patrol car may drive around a public parking lot capturing hundreds of vehicles’ plates in minutes.
ALPR Databases
Most of this ALPR data is stored in databases for extended periods of time—often as much as five years. The databases may be maintained by the police departments, but often they are maintained by private companies such as Vigilant Technologies. Law enforcement agencies without their own ALPR systems can access data collected by other law enforcement agencies through regional sharing systems and networks operated by these private companies. Several companies operate independent, non-law enforcement ALPR databases, contracting with drivers to put cameras on private vehicles to collect the information. These data are then sold to companies like insurers, but law enforcement can also purchase access to this commercial data on a subscription basis.
Hotlists
Law enforcement agencies will often pre-load a list of license plates that the ALPR system is actively looking for—such as stolen vehicles and vehicles associated with outstanding warrants. Police officers can also create their own hotlists. If the ALPR camera scans a plate on the list, the system sends an alert to the officer in the squad car (if it’s a mobile reader) or the agency (if it’s a fixed reader). Some hotlists include low-level misdemeanors and traffic offenses. Some agencies use these hotlists to generate revenue by stopping citation scofflaws.
What Kinds of Data ALPRs Collect
ALPRs collect license plate numbers and location data along with the exact date and time the license plate was encountered. Some systems are able to capture make and model of the vehicle. They can collect thousands of plates per minute. One vendor brags that its dataset includes more than 6.5 billion scans and grows at a rate of 120-million data points each month.
When combined, ALPR data can reveal the direction and speed a person traveled through triangulation. In aggregate over time, the data can reveal a vehicle’s historical travel. With algorithms applied to the data, the systems can reveal regular travel patterns and predict where a driver may be in the future. The data also reveal all visitors to a particular location.
The data generally does not include the driver’s name. However, law enforcement officers can use other databases to connect individual names with their license plate numbers.
In addition to capturing license plate data, the photographs can reveal images of the vehicle, the vehicle’s drivers and passengers, as well as its immediate surroundings—and even people getting in and out of a vehicle. A 2009 privacy impact assessment report indicates that the photographs may even include bumper stickers, which could reveal information on the political or social views of the driver.
How Law Enforcement Uses ALPRs

Law enforcement has two general purposes for using license plate readers.
Real-time investigations
By adding a license plate to a “hot list,” officers can use ALPR to automatically identify or track particular vehicles in real time. Licenses plates are often added to hot lists because the vehicle is stolen or associated with an outstanding warrant. Officers may also add a plate number to the list if the vehicle has been seen at the scene of a crime, the owner is a suspect in a crime, or the vehicle is believed to be associated with a gang. Hot lists often include low-level offenses, too.
Historical investigations
Since ALPRs typically collect information on everyone—not just hot-listed vehicles—officers can use a plate, a partial plate, or a physical address to search and analyze historical data. For example, an officer may enter the location of a convenience store to identify vehicles seen nearby at the time of a robbery. The officer can then look up those plate numbers to find other locations that plate has been captured.
Training materials, policies and laws in some jurisdictions instruct officers that a hot-list alert on its own may not be enough to warrant a stop. Officers are instructed to visually confirm that a plate number is a match. Failure to manually confirm, combined with machine error, has caused wrongful stops.
Law enforcement claims that ALPR data has been used to, for example, recover stolen cars or find abducted children. However, police have also used ALPR data for mass enforcement of less serious offenses, such as searching for uninsured drivers or tracking down individuals with overdue court fees.
The ACLU estimates that less than 0.2 percent of plate scans are linked to criminal activity or vehicle registration issues. Many law enforcement agencies store ALPR data for years, and share it with other law enforcement agencies and federal agencies.
The length of time that ALPR data is retained varies from agency to agency, from as short as mere days to as long as several years, although some entities—including private companies—may retain the data indefinitely.
Who Sells ALPR Technology
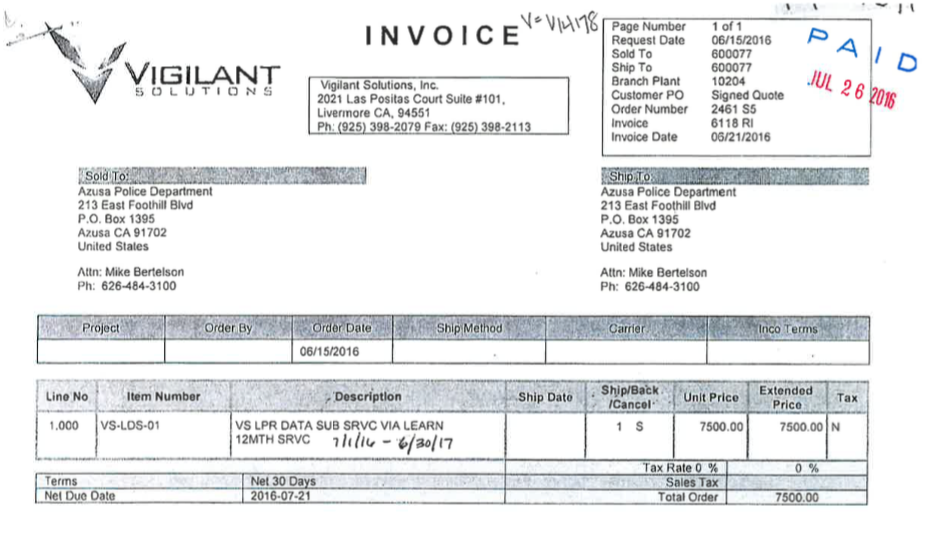
Vigilant Solutions’ subsidiary Digital Recognition Network, along with MVTrac, are the two main companies hiring contractors to collect ALPR data across the country. The companies then share the commercially-collected data not just with law enforcement but also with auto recovery (aka “repo”) companies, banks, credit reporting agencies, and insurance companies. Data collected by private entities does not have retention limits and is not subject to sunshine laws, or any of the other safeguards that are sometimes found in the government sector.
Some jurisdictions use ALPR technology originally developed by PIPS, which was subsequently sold to 3M. The ALPR division was more recently acquired by Neology, Inc.
Threats Posed by ALPR
ALPR is a powerful surveillance technology that can be used to invade the privacy of individuals as well as to violate the rights of entire communities.
Law enforcement agencies have abused this technology. Police officers in New York drove down a street and electronically recorded the license plate numbers of everyone parked near a mosque. Police in Birmingham targeted a Muslim community while misleading the public about the project. ALPR data EFF obtained from the Oakland Police Department showed that police disproportionately deploy ALPR-mounted vehicles in low-income communities and communities of color.
Moreover, many individual officers have abused law enforcement databases, including license plate information and records held by motor vehicle departments. In 1998, a Washington, D.C. police officer “pleaded guilty to extortion after looking up the plates of vehicles near a gay bar and blackmailing the vehicle owners.” Police officers have also used databases to search romantic interests in Florida. A former female police officer in Minnesota discovered that her driver’s license record was accessed 425 times by 18 different agencies across the state.
In addition to deliberate misuse, ALPRs sometimes misread plates, leading to dire consequences. In 2009, San Francisco police pulled over Denise Green, an African-American city worker, handcuffed her at gunpoint, forced her to her knees, and searched both her and her vehicle—all because her car was misidentified as stolen due to a license plate reader error. Her experience led the U.S. Ninth Circuit Court of Appeals to rule that technology alone can’t be the basis of such a stop, but that judgment does not apply everywhere, leaving people vulnerable to similar law enforcement errors.
Aggregate data stored for lengthy periods of time (or indefinitely) becomes more invasive and revealing, and it is susceptible to both misuse and data breach. Sensible retention limits, specific policies about who inside an agency is allowed to access data, and audit and control processes could help minimize these issues. One of the better privacy protections would be for police to retain no information at all when a passing vehicle does not match a hot list.
EFF’s Work on ALPR
EFF has been investigating and combating the privacy threats of ALPR technology through public records requests, litigation, and legislative advocacy since 2012.
ALPR Litigation
EFF and the ACLU of Southern California sued the Los Angeles County Sheriff’s Department and the Los Angeles Police Department after the agencies refused to hand over ALPR data. The agencies claimed the records were exempt from the California Public Records Act because they were investigative records. This argument amounts to claiming that all Los Angelenos are under investigation, a point that both a lawyer for the LAPD and a California Supreme Court Justice agreed sounded “Orwellian” during oral arguments. In 2017, the California Supreme Court ruled in EFF and ACLU’s favor and ordered the case back to the Superior court.
Outside of California, EFF has filed briefs in a lawsuit over the excessive storage collection of ALPR data in the state of Virginia.
ALPR Accountability and Transparency
In 2015, the California legislature passed S.B. 34, a bill that requires ALPR users to protect data, maintain access logs, hold public meetings before starting an ALPR program, implement a usage and privacy policy, and maintain access logs. The law also prohibits public agencies from selling, sharing, or transferring ALPR data except to other public agencies.
EFF has coordinated volunteers to collect ALPR policies across the state of California and to expose agencies failing to comply with the law. EFF has also independently filed public records requests with dozens of agencies to shine light on their use of ALPR data.
ALPR Security
EFF investigated more than 100 ALPR cameras operated by law enforcement that were leaking data because of misconfiguration. These cameras were inadvertently publicly accessible through web browsers and Telnet interfaces. After EFF disclosed these vulnerabilities, several agencies in Louisiana and California overhauled their ALPR networks.
We have also contacted public safety agencies whose ALPR data was exposed online, often on websites accessible to anyone with a web browser, to responsibly disclose the security vulnerabilities we found.